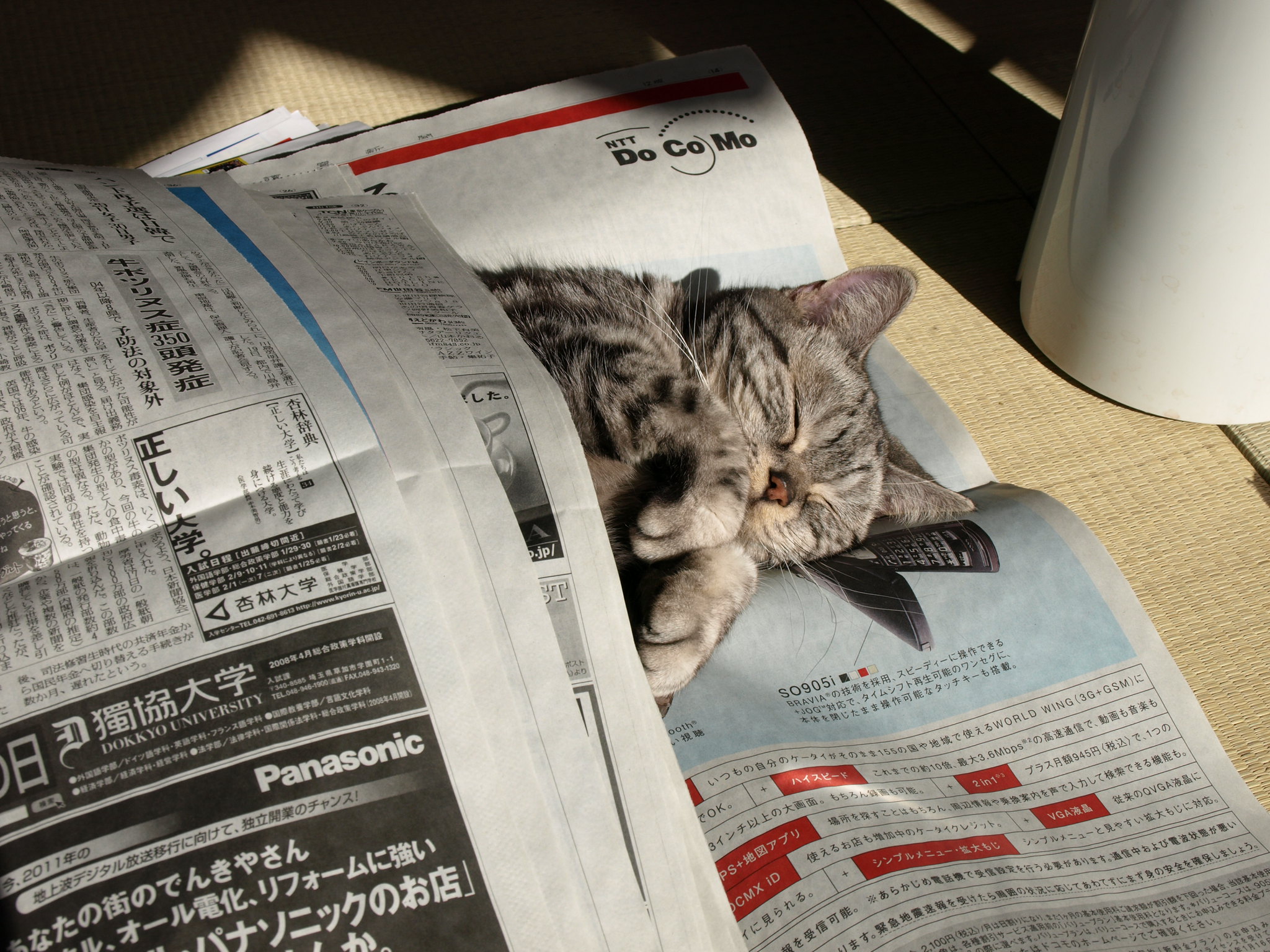
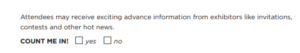
Welcome to this week’s Tip of the Hat! It seems that spring has just arrived for many of us in the US; however, the calendar tells us that we are only weeks away from the ALA Annual Conference in Washington DC in June. Our Executive Assistant was going through the PDF registration form the other day and noticed the following question:
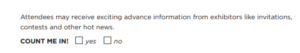
The above question on the registration form asks if the person (or in this case, cat) wants to receive information from conference exhibitors. The Executive Assistant paused. What does checking the “Yes” box all entail? Since we’re in the data privacy business, this is a perfect Monday Mystery for us to investigate.
After a quick search of the conference website, we land on ALA’s Privacy Policy at http://www.ala.org/privacypolicy. If you haven’t spent time with a privacy policy, it can seem daunting or downright boring. Let’s walk through this policy to find out what happens when we check the “Yes” box.
The “Information Collection & Use” section lays out what information is collected and when. They define “personal data” as information that can be used to identify someone: name, email, address, etc. The section breaks down some common actions and situations when ALA collects data, including event registration. We already guessed that ALA was collecting our information for event registration purposes, but we need to dig deeper into the policy to answer our question.
We then find a section labeled “Information Sharing” in which we might find our answer! The section lists who ALA shares information with in detail, including the type of data and circumstances that the data is shared. “Services Providers” seems promising – that is until we get into the details. The data listed that is shared to service providers is mostly technical data – location data, log files, and cookies – and has nothing regarding giving information to receive updates from exhibitors. Back to square one.
Moving down the policy, we arrive at the “Your Rights and Choices Regarding Your Information” section, which lists the following right:
“Object to processing – You have the right to object to your Personal Data used in the following manners: (a) processing based on legitimate interests or the performance of a task in the public interest/exercise of official authority (including profiling); (b) direct marketing (including profiling); and (c) processing for purposes of scientific/historical research and statistics;”
Okay, we have the right to ask ALA not to use our personal data for marketing purposes. That’s a very important right to have, though that doesn’t exactly solve the mystery of what happens when we click on the “Yes” box.
This, readers, is where we are going to cheat in this investigation. It’s time to put our exhibitor hat on!
Exhibitors at major conferences are usually offered some form of registrant/member list as a means to promote their business before the conference. ALA does the same with Annual, and exhibitors can rent attendee lists. From https://2019.alaannual.org/list-rental, exhibitors have the option to “[t]arget buyers by industry segment, demographic profile or geographic area.” So, just not names and emails are shared!
On the exhibitor side, having that information would allow for targeted marketing – instead of blasting the entire attendee list, exhibitors can reach out to those most likely to be receptive to their service or product. On the attendee side, some want to have this type of targeted marketing to plan their time at the conference efficiently, or to do homework before hitting the exhibit hall. For other attendees, though, it means more emails that they’ll just delete or unsubscribe. And then there’s the question about what happens to that attendee data after the conference…
In the end, we still have a bit of a mystery on our hands. The only reason we got this far in our little Monday Mystery investigation is that LDH has been bombarded with emails trying to sell us attendee lists which tipped us off to start looking at the exhibitor section of the conference site. Your average conference attendee wouldn’t have that information and would be left scratching their heads due to the lack of information at the point of registration about what information is shared on these attendee lists. While we don’t have a clear answer to end today’s investigation, we hope that this gives our readers a little reminder to do some research the next time they are asked a similar question on a registration form.
Speaking of ALA Annual, LDH Consulting Services is excited to announce that we will be exhibiting in DC in booth 844! Many thanks to Equinox Open Library Initiative for making exhibiting at ALA Annual possible for LDH. Give us a ping if you will be at Annual and would like to talk more about LDH can do for your organization.