Welcome back to the third installment of the information fiduciaries and libraries series! It’s been a while since we explored the concept of libraries acting as a trusted party managing patron personal data. Thanks to Tessa Walsh’s recent demo of Bulk Reviewer, we got the nudge we needed to tackle part three of the series. You can catch up on Parts One and Two if you need a refresher on the subject.
Managing Personal Data in a Collection
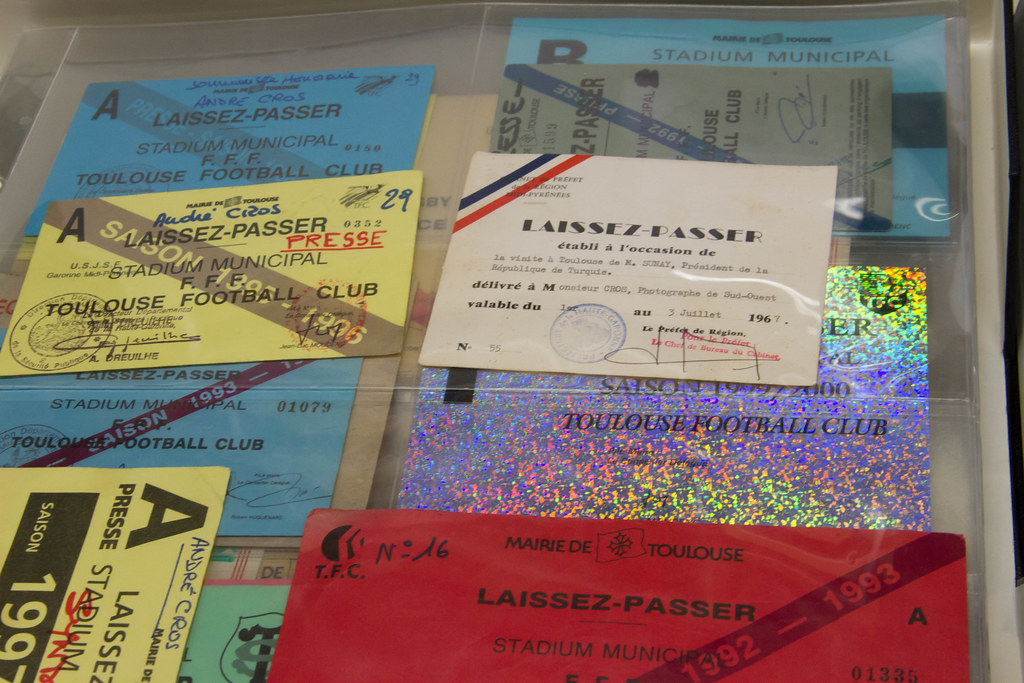
We left off the series with the question about what happens to a library’s information fiduciary role when the personal data is entrusted with is part of the collection. The relationship between the personal data in the collection, the person, and the library or archive is not as straightforward as the relationship between the library and the patron generating data from their use of the library. Personal papers and collections donated to archives contain different types of personal data, from financial and medical to personal secrets. What happens in the case where a third party donates these papers containing highly personal information about another person to a library or archive? In the case of a person donating their documents, what happens when they have personal data of another person who may not have consented to have this data included in this donation? Moving from the archive to the institutional repository, what happens when a researcher submits research data that contain identifiable personal data as part of a data set, be it a spreadsheet that includes Social Security Numbers or oral histories containing highly personal information to a living person?
As you probably already guessed, these complications are only the start of the fiduciary responsibilities of libraries and archives surrounding these types of personal data. We’ve covered redacting PII from digital collections in the past, but redaction of personal data to protect the privacy of the people behind that data only addresses a small part of how libraries and archives can fulfill their information fiduciary role. Managing personal data in collections requires managing data in the best interests of the library/archive and the person donating the materials and the best interests of the people behind the personal data included in that donated material, which may not be the same person as the donor.
Thankfully, we don’t have to navigate this complex web of relationships to determine how to manage the collection with the best interest of the people behind the data. The Society of American Archivist’s Privacy & Confidentiality Section can help libraries and archives manage personal data in their collections. If you are looking for documentation around privacy in archives, check out the documentation portal. Have too many types of personal data to know where to start? The section’s bibliography can lead you to the right resources for each major type of personal information you have in your collection. Perhaps you want to know more about current issues and concerns around personal data in collections. The RESTRICTED blog has you covered, alongside webinars such as Tessa’s demo of Bulk Reviewer mentioned at the start of this post. We highly recommend checking out the mini-blog series from Heather Briston, following up on her webinar “It’s Not as Bad as You Think – Navigating Privacy and Confidentiality Issues in Archival Collections.”
Beyond the section, you also might find the following publications helpful in determining how your library or archive should fulfill their responsibilities to the people behind the data in your collections:
- Botnick, Julie. “Archival Consent.” InterActions: UCLA Journal of Education and Information Studies 14, no. 2 (2018). https://doi.org/10.5070/D4142038539.
- Mhaidli, Abraham, Libby Hemphill, Florian Schaub, Cundiff Jordan, and Andrea K. Thomer. “Privacy Impact Assessments for Digital Repositories.” International Journal of Digital Curation 15, no. 1 (December 30, 2020): 5. https://doi.org/10.2218/ijdc.v15i1.692.
This is only a small selection of what’s available, but the Privacy & Confidentiality Section’s resources are an excellent place to start to untangle the complex web of determining what is in the best interest of all parties involved in managing the personal data in your collections.
Before we end our post, there is one question that a few of our readers might have – can archivists guarantee the same level of confidentiality as lawyers or doctors can in protecting personal information in legal matters?
A Question of Archival Privilege
Some of our readers might remember discussions about archival privilege in the early 2010s stemming from the litigation surrounding the Belfast Project oral histories. Archival privilege is not legally recognized despite legal arguments for such a privilege or tying such a privilege to researcher privilege in court (such as in Wilkinson v. FBI and Burka v. HHS). These rulings mean that materials in a collection are subject to search via subpoenas and warrants, which leads to privacy harms to those whose personal data is included in those collections. Nevertheless, it’s still worthwhile to revisit the calls for such a privilege and discussions of what archival privilege would look like:
- Dooley, Jackie. “Should a Legal Right to ‘Archival Privilege’ Be Established?” Off the Record (blog), February 14, 2013. https://offtherecord.archivists.org/2013/02/14/should-a-legal-right-to-archival-privilege-be-established/.
- George, Christine. “Archives Beyond the Pale: Negotiating Legal and Ethical Entanglements after the Belfast Project.” The American Archivist 76, no. 1 (May 27, 2013): 47–67. https://doi.org/10.17723/aarc.76.1.x34p8k7848512274.
Even though Boston College successfully appealed the initial order to hand over all the records listed in the subpoena, we are still left with whether the archives profession should push for privileged relationships between donors or other individuals represented in the collections and the archives. We will leave discussion of if such a privilege should exist (and in what form) to our readers.